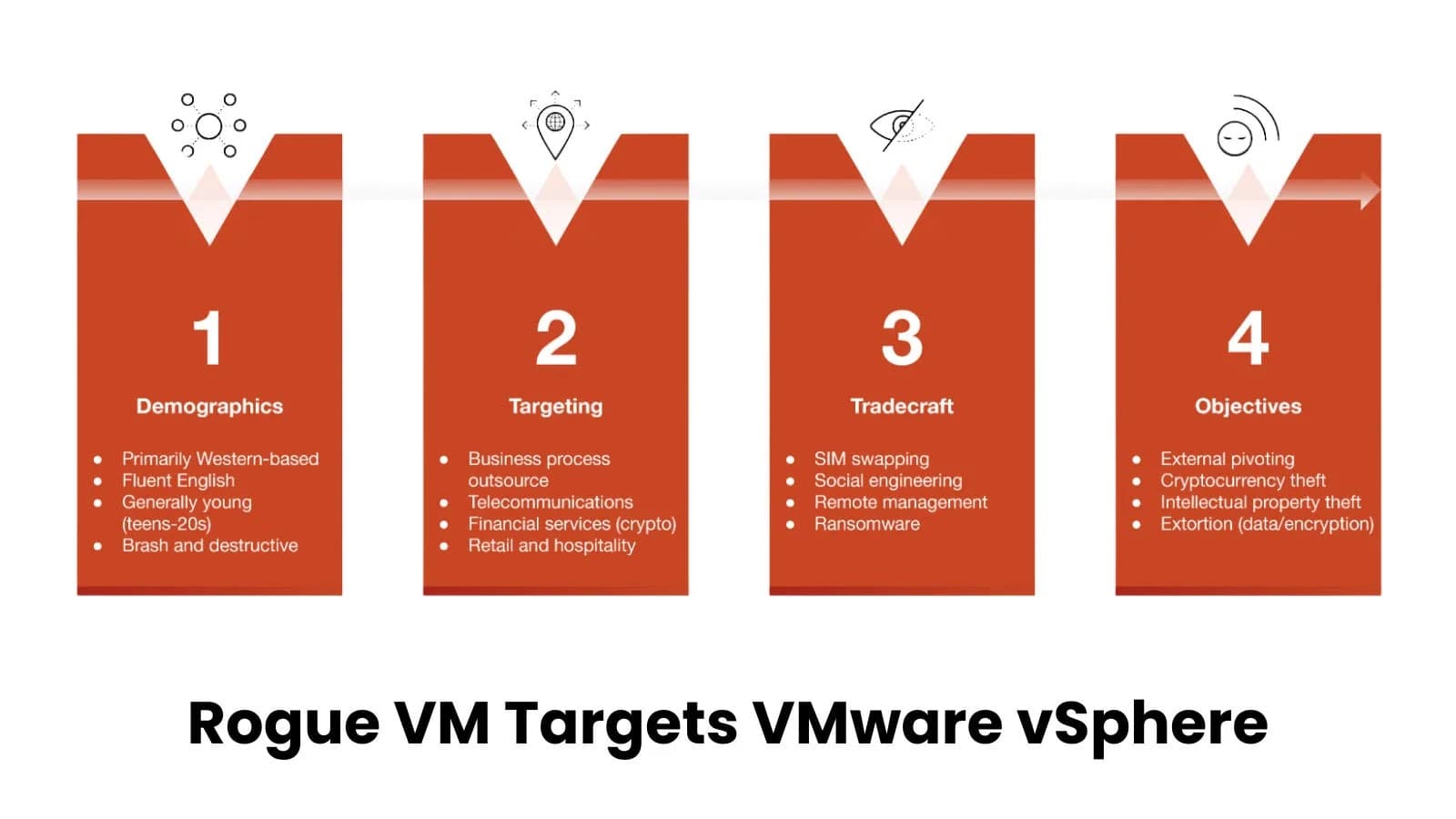
Arogue virtual machines (VMs) were a key component of the cybercrime group Muddled Libra's (also known as Scattered Spider or UNC3944) attack on VMware vSphere environments This article explores unc3944 attack vmware. . This incident, which was discovered during an investigation in September 2025, provides a unique look into the group's operational methods and illuminates its tactics, techniques, and procedures (TTPs).
Taking advantage of VMware vSphere The attack started when Muddled Libra entered a targeted VMware vSphere environment without authorization. The attackers swiftly created a new virtual machine (VM) after gaining access to the system in order to avoid endpoint security tools. This virtual machine acted as a beachhead for additional malevolent actions, such as lateral movement, reconnaissance, and attack tool downloads.
In order to stay persistent in the environment, the attackers used the Chisel tunneling tool to create a command-and-control (C2) channel using stolen certificates. Unit 42's investigation of the attack's high-level chain of events (Source: paloaltonetworks) They started by shutting down virtualized domain controllers (DCs) and making copies of important files, such as the SYSTEM registry hives and NTDS.dit file, which hold hashed passwords for every user. By taking this action, the group was able to increase their level of access and obtain data for future exploitation.
The group sought out vital services for possible exploitation, such as Veeam, MSSQL, and Exchange, and downloaded and used a range of tools to engage with the target's infrastructure during the attack, including the ADRecon tool for Active Directory enumeration.
URL that hosts the Chisel tool archive (Source: paloaltonetworks) Additionally, they accessed Snowflake data, most likely to find private information to exfiltrate. Perspectives on Muddled Libra's Strategies Muddled Libra is renowned for its nuanced strategy, which uses social engineering and legal tools to carry out attacks. In this instance, they exfiltrated stolen data using tools like S3 Browser and PsExec for lateral movement.
To evade detection, they take advantage of the environment's built-in infrastructure rather than depending on complex malware. They can keep a low profile while achieving their goals thanks to this strategy, which is referred to as living off the land.
Goon.zip, the tool that was downloaded (Source: paloaltonetworks) The use of web searches by the attackers to find possible data of interest was one of the investigation's main conclusions. For instance, in order to determine the business sector of the organization and potentially find useful data to target, they looked up the North American Industry Classification System (NAIC) code. Additionally, the group uploaded files to cloud storage services like Dropbox and LimeWire, demonstrating persistence in their attempts to exfiltrate data.
Additionally, they carried out troubleshooting tasks like investigating Outlook problems and downloading Personal Storage Table (PST) files and accessing mailboxes using OfficeSetup.exe. This attack emphasizes how crucial it is to uphold robust identity security and implement stringent access controls.
The strategies used by Muddled Libra show how a straightforward rogue virtual machine can act as a base for persistent access, data theft, and extensive lateral movement. Organizations are reminded by the attack to implement a defense-in-depth approach, with an emphasis on: enhancing identity security with user access control and multi-factor authentication (MFA). keeping an eye out for unusual activity, particularly when using administrative tools.
identifying and stopping living-off-the-land behaviors, which are just as dangerous as conventional malware-based attacks but frequently more difficult to detect. Paloalt Onet Works claims that in order to reduce the harm caused by compromised credentials, the incident also emphasizes the necessity of ongoing cloud environment monitoring and the implementation of least-privilege access controls. Organizations can improve their readiness to combat these advanced threats by taking a cue from Muddled Libra's strategies.











.webp%3Fw%3D1068%26resize%3D1068%2C0%26ssl%3D1&w=3840&q=75)