Cybersecurity for another week. One more week of "you've got to be kidding me." The attackers were occupied.
The defenders were occupied. Many people had a terrible Monday morning somewhere in the middle. That's just the way things are these days. Unleases from Transparent Tribe Vibeware Against Indian Entities — Transparent Tribe, a threat actor affiliated with Pakistan, has used artificial intelligence (AI)-powered coding tools to vibe-code malware and target the Indian government and its embassies abroad in a recent attack campaign that Bitdefender discovered.
To avoid detection, these tools are written in specialized programming languages like Nim, Zig, and Crystal.
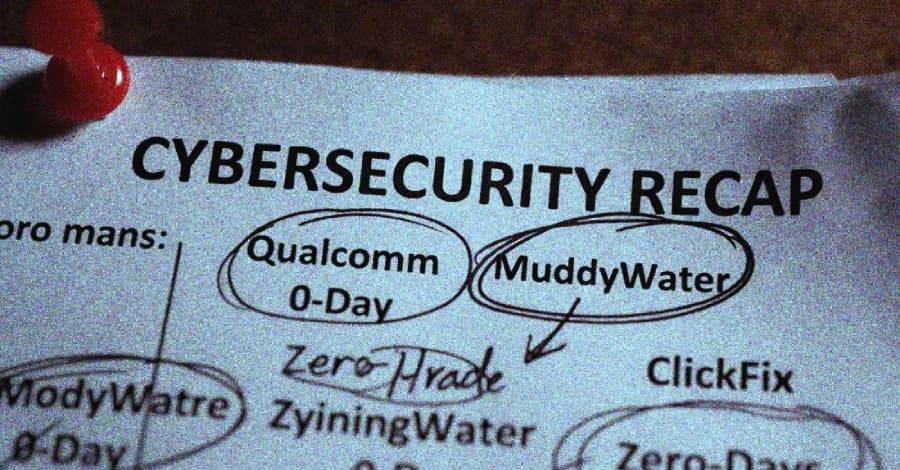
"Rather than a breakthrough in technical sophistication, we are seeing a transition toward AI-assisted malware industrialization that allows the actor to flood target environments with disposable, polyglot binaries," the company said. Iranian Hackers Target U.S. Entities Amid Conflict — The Iranian hacking group tracked as MuddyWater (aka Seedworm) targeted several U.S.
This webinar breaks down what that means for security, and what you actually need to do before something goes wrong. ## 📰 Around the Cyber World ## 🔧 Cybersecurity Tools DetectFlow → It is an open-source detection pipeline from SOC Prime that matches streaming log events against Sigma rules in real time — before they ever reach your SIEM.
It uses Apache Kafka and Flink to tag and enrich events in-flight, then passes the results downstream to where you need them, rather than depending on your SIEM to do the heavy lifting. It is intended for teams that desire quicker detection, greater rule coverage, and less reliance on SIEM-imposed limits. It is based on 11 years of detection intelligence.
ADTrapper → is an open-source platform that uses 54+ built-in detection rules to analyze Windows Active Directory authentication logs and identify threats, ranging from brute force to AD CS attacks.