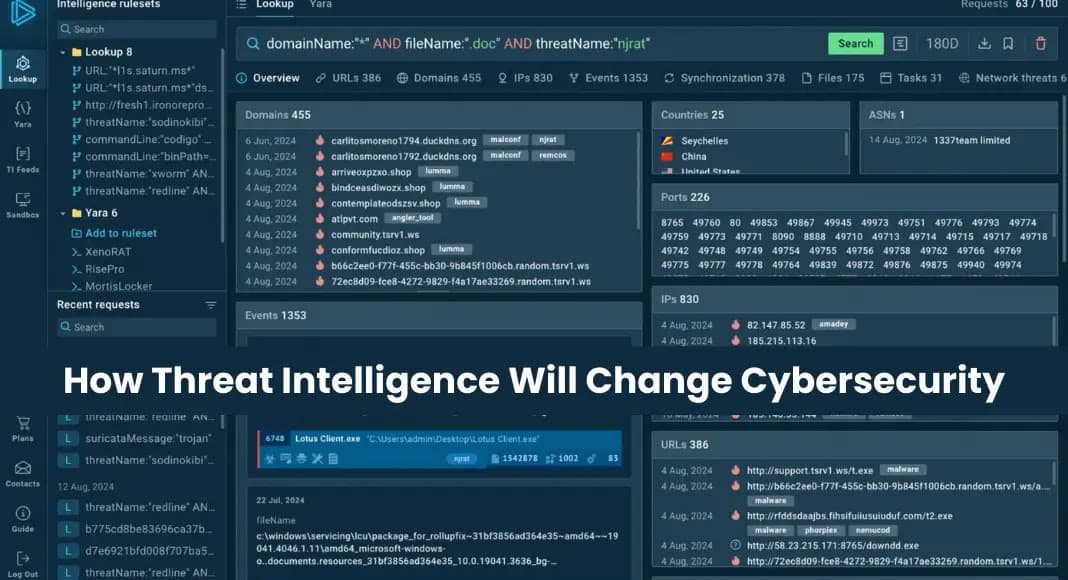
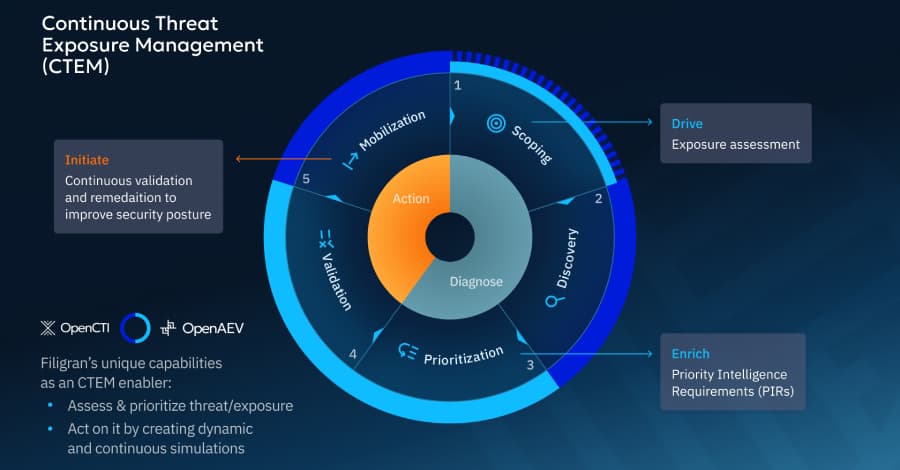
How Threat Intelligence Will Change Cybersecurity in 2026
As 2026 approaches, the cybersecurity environment is changing in ways that are actually advantageous to defenders This article explores 2026
How Threat Intelligence Will Change Cybersecurity in 2026
As 2026 approaches, the cybersecurity environment is changing in ways that are actually advantageous to defenders This article explores 2026


%2520(1).webp&w=3840&q=75)


%2520(1).webp&w=3840&q=75)
%2520(1).webp&w=3840&q=75)







