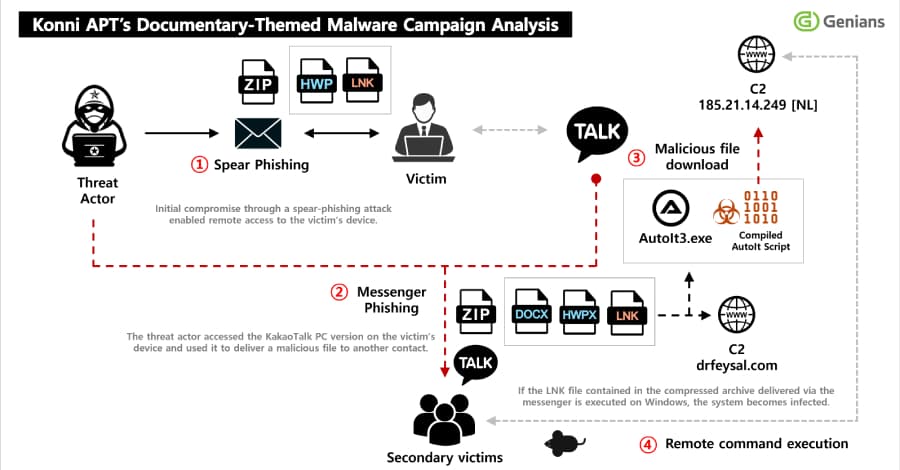
North Korean hackers have been seen sending phishing emails to get into people's KakaoTalk desktop apps and spread malware to some of their contacts This article explores korean hackers seen. . South Korean threat intelligence company Genians says that the activity was caused by a hacking group known as Konni.
"An email that looked like a notice appointing the recipient as a North Korean human rights lecturer was used to get initial access," the Genians Security Center (GSC) said in an analysis.After the spear-phishing attack worked, the victim opened a bad LNK file, which infected their computer with remote access malware.
The malware stayed hidden and active on the victim's endpoint for a long time, stealing sensitive information and internal documents. "The threat actor is said to have stayed on the compromised host for a long time, using the unauthorized access to steal internal documents and the KakaoTalk app to spread the malware to certain contacts. The attack is interesting because it takes advantage of the trust that compromised victims have in order to trick and trap more people.
Konni has used the messaging app to spread things before.
In November 2025, the hacking group was found to be using signed-in KakaoTalk chat app sessions to send malicious ZIP files to victims' contacts while also remotely wiping their Android devices using stolen Google credentials. The latest attack campaign starts with a spear-phishing email that tries to get people to open a ZIP file attachment that has a Windows shortcut (LNK) in it. When the LNK file runs, it downloads a next-stage payload from an outside server, sets up persistence with scheduled tasks, and finally runs the malware.
It also shows the user a PDF decoy document to keep them from noticing what is really happening.
The downloaded malware is a remote access trojan (RAT) called EndRAT (also known as EndClient RAT) that was written in AutoIt. It lets the operator take control of the compromised host from afar by giving them access to files, a remote shell, data transfer, and persistence. A closer look at the infected host has revealed the presence of several malicious artifacts, such as AutoIt scripts for RftRAT and RemcosRAT.
This shows that the attacker thought the victim was important enough to drop multiple RAT families to make them more resilient. A key part of the attack is that the bad actor used the victim's KakaoTalk app on the infected system to send ZIP files with malware to other people on their contact list and install the same malware.
This basically makes current victims into people who help with more attacks. Genians said, "This campaign is seen as a multi-stage attack operation that goes beyond simple spear-phishing and includes long-term persistence, information theft, and account-based redistribution." The actor picked certain people from the victim's friend list and sent them more harmful files.
The attacker used file names that looked like materials that introduced North Korea-related content to get people to open the files.