Attackers Take Over Canadian Digital Services, Putting Millions of Users at Risk
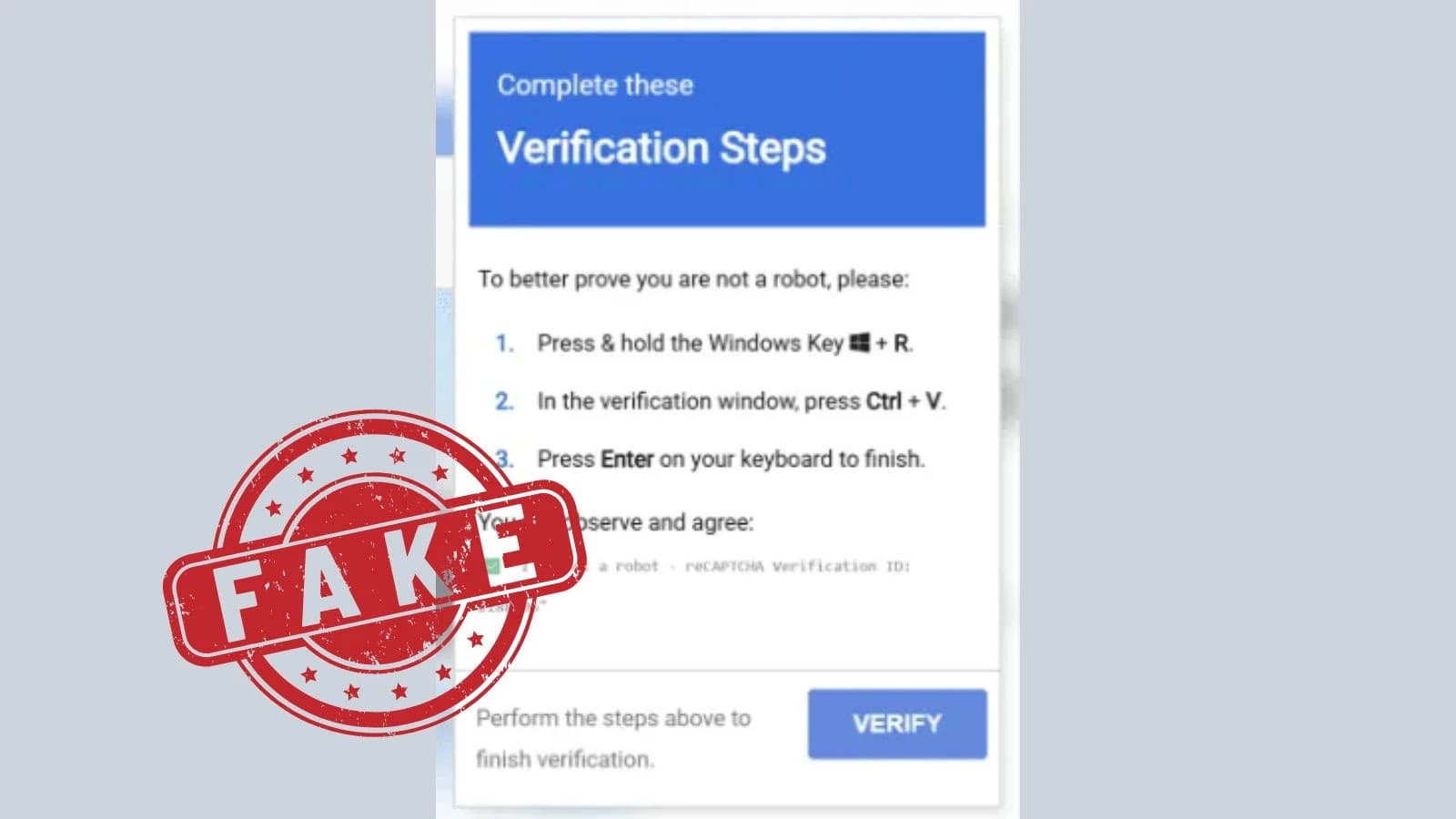
Because of their heavy reliance on digital services for travel, taxes, packages, and traffic fines, Canadian citizens are increasingly at risk from

Attackers Take Over Canadian Digital Services, Putting Millions of Users at Risk
Because of their heavy reliance on digital services for travel, taxes, packages, and traffic fines, Canadian citizens are increasingly at risk from


%2520to%2520Deploy%2520Malware.png%3Fw%3D696%26resize%3D696%2C0%26ssl%3D1&w=3840&q=75)