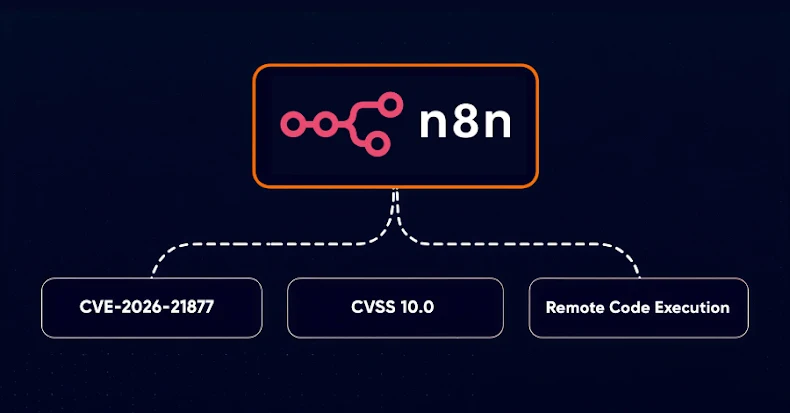
n8n Warns of CVSS 10.0 RCE Vulnerability Affecting Self-Hosted and Cloud Versions
A maximum-severity security vulnerability that, if successfully exploited, could lead to authenticated remote code execution (RCE) has been reported by n8n. The vulnerability is rated 10.0
n8n Warns of CVSS 10.0 RCE Vulnerability Affecting Self-Hosted and Cloud Versions
A maximum-severity security vulnerability that, if successfully exploited, could lead to authenticated remote code execution (RCE) has been reported by n8n. The vulnerability is rated 10.0