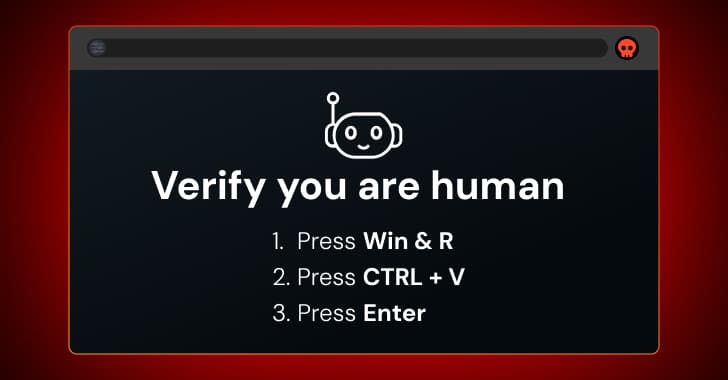
China-Linked Hackers Exploit Windows Shortcut Flaw to Target European Diplomats
A new series of attacks that take advantage of an unpatched Windows shortcut vulnerability have been connected to a threat actor with ties to China. Between September and October of 2025, Eur
China-Linked Hackers Exploit Windows Shortcut Flaw to Target European Diplomats
A new series of attacks that take advantage of an unpatched Windows shortcut vulnerability have been connected to a threat actor with ties to China. Between September and October of 2025, Eur