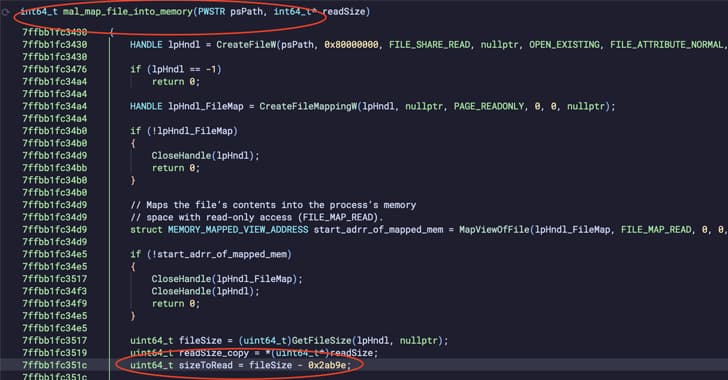
Russian Hackers Gamaredon and Turla Collaborate to Deploy Kazuar Backdoor in Ukraine
Gamaredon and Turla, two Russian hacking groups, are working together to target and co-compete with Ukrainian entities. Both organizations are thought to be connected to the Russian Federal S
Russian Hackers Gamaredon and Turla Collaborate to Deploy Kazuar Backdoor in Ukraine
Gamaredon and Turla, two Russian hacking groups, are working together to target and co-compete with Ukrainian entities. Both organizations are thought to be connected to the Russian Federal S