New SparrowDoor Backdoor Variants Found in Attacks on U.S. and Mexican Organizations
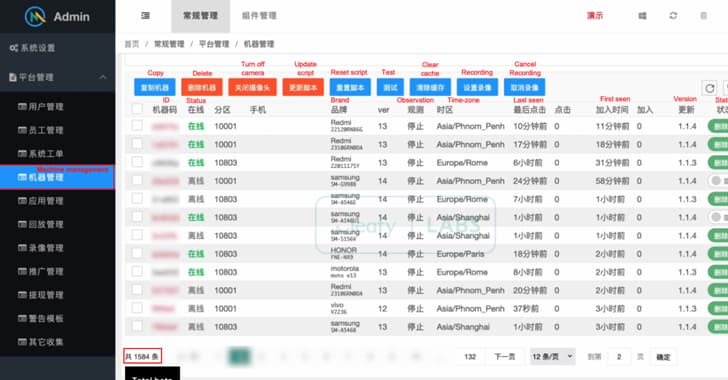
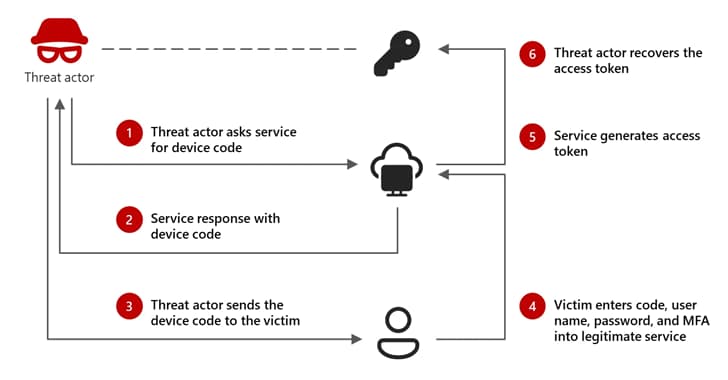
FamousSparrow is connected to a cyberattack that targeted a Mexican research institute and a trade association in the United States. The threat actor launches a web shell on an Internet Infor

New SparrowDoor Backdoor Variants Found in Attacks on U.S. and Mexican Organizations
FamousSparrow is connected to a cyberattack that targeted a Mexican research institute and a trade association in the United States. The threat actor launches a web shell on an Internet Infor