Smooth Sailing or Big Breach? The Mexican government is accused of leaking
After a hacktivist group leaked 2.3TB of data online, the information of over a quarter (28%) of Mexico's population may be at risk This article

Smooth Sailing or Big Breach? The Mexican government is accused of leaking
After a hacktivist group leaked 2.3TB of data online, the information of over a quarter (28%) of Mexico's population may be at risk This article
















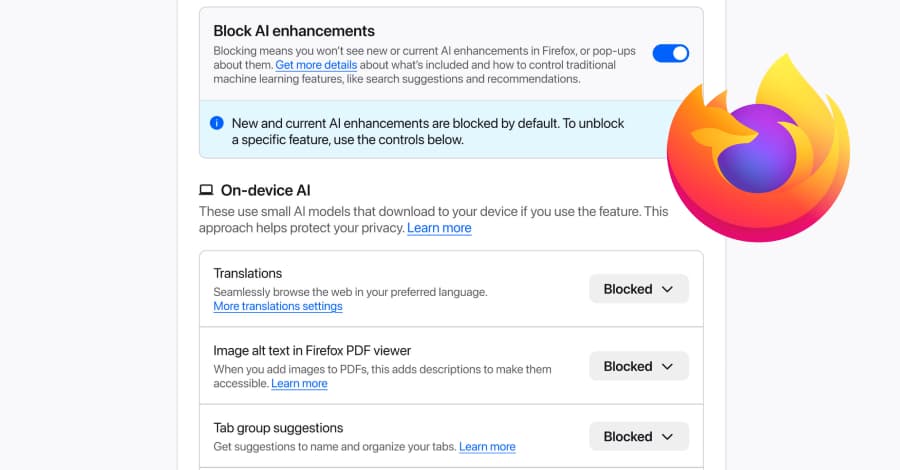
![[Webinar] The Smarter SOC Blueprint: Learn What to Build, Buy, and Automate](/_next/image?url=https%3A%2F%2Fblogger.googleusercontent.com%2Fimg%2Fb%2FR29vZ2xl%2FAVvXsEiwD8GAdNdNuHeeaGY_XNzQ5R2ImwMvVU46K5gM8t9-q0vuQ4enqi1W5Ljd4D6RktNyAY75SA0gLSrf6oqykbq3lQn5jhZglmqyGYGf3pm6mdHbTSjZoRxPFxG3ruwjYGu6vl9UtgAaORZTIkEliQl1bzeWXt554RsrCKzJlAhyADYV2X_n42rmfAg_Iiig%2Fs1700-e365%2Fsoc.jpg&w=3840&q=75)