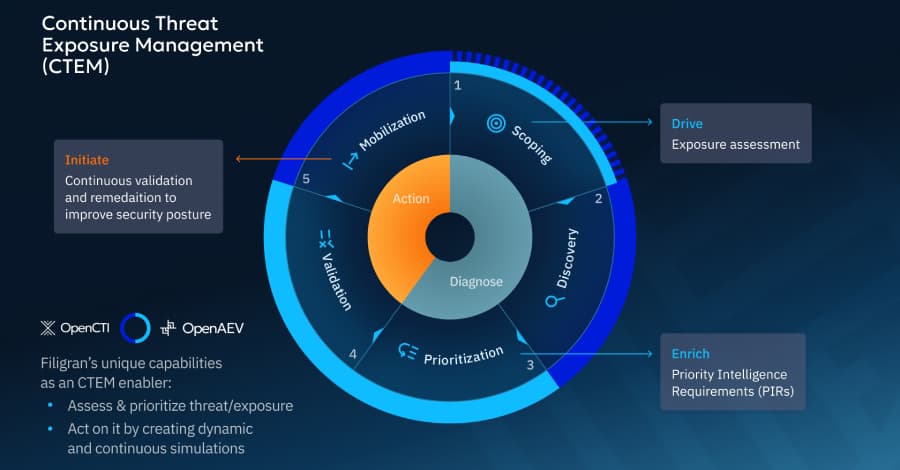
CTEM in Practice: Outcomes That Matter, Validation, and Prioritization
There is a growing desire among cybersecurity teams to go beyond examining threats and vulnerabilities separately This article explores examining
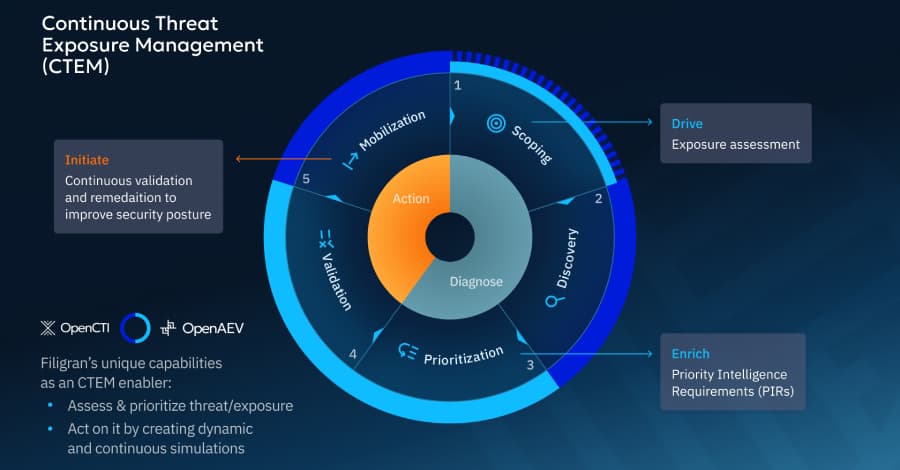
CTEM in Practice: Outcomes That Matter, Validation, and Prioritization
There is a growing desire among cybersecurity teams to go beyond examining threats and vulnerabilities separately This article explores examining



_Blackboard_Alamy.jpg%3Fwidth%3D1280%26auto%3Dwebp%26quality%3D80%26format%3Djpg%26disable%3Dupscale&w=3840&q=75)