The Case for Dynamic AI-SaaS Security as Copilots Scale
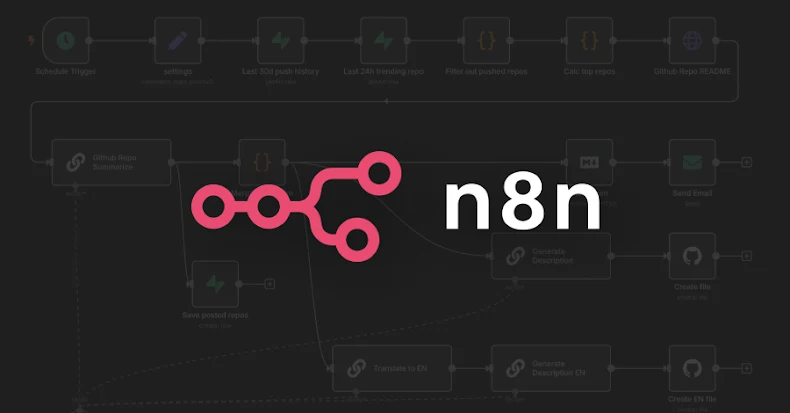
Artificial intelligence copilots and agents have subtly infiltrated the SaaS apps that companies use on a daily basis during the past year. AI assistants or agent-like features are now integr

The Case for Dynamic AI-SaaS Security as Copilots Scale
Artificial intelligence copilots and agents have subtly infiltrated the SaaS apps that companies use on a daily basis during the past year. AI assistants or agent-like features are now integr