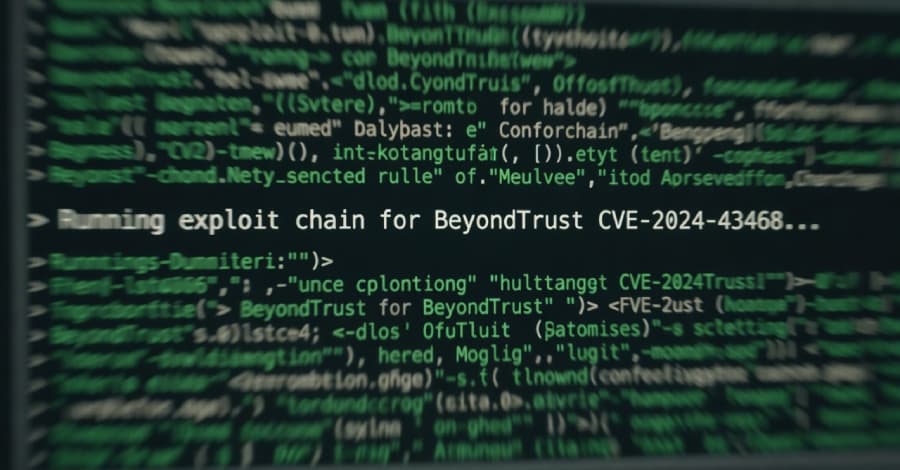
In the most recent KEV update, CISA identifies four security flaws that are being actively exploited.
Citing evidence of active exploitation in the wild, the U.S This article explores vulnerability known cve. . Cybersecurity and Infrastructure Security.

In the most recent KEV update, CISA identifies four security flaws that are being actively exploited.
Citing evidence of active exploitation in the wild, the U.S This article explores vulnerability known cve. . Cybersecurity and Infrastructure Security.