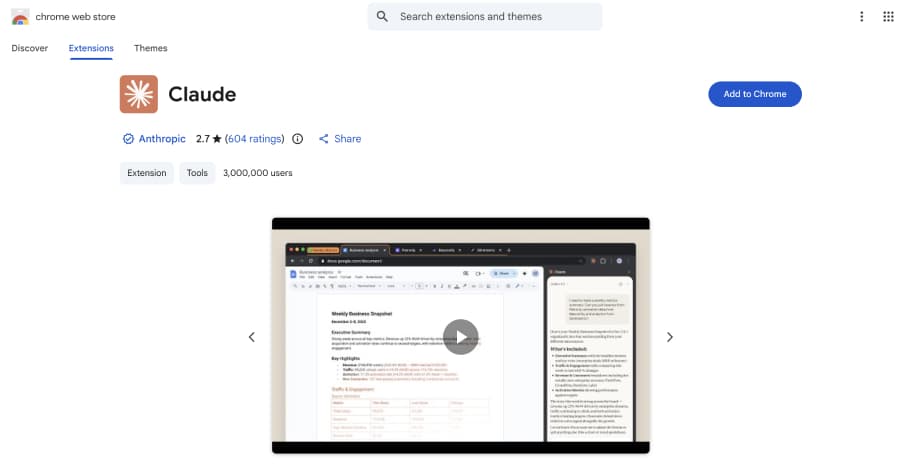
Claude Extension Flaw Enabled Zero-Click XSS Prompt Injection via Any Website
Discover how People could have used Anthropic's Claude Google Chrome Extension to send bad prompts. The problem is caused by two underlying flaws: an.
Claude Extension Flaw Enabled Zero-Click XSS Prompt Injection via Any Website
Discover how People could have used Anthropic's Claude Google Chrome Extension to send bad prompts. The problem is caused by two underlying flaws: an.




![[Webinar] Stop Guessing. Learn to Validate Your Defenses Against Real Attacks](/_next/image?url=https%3A%2F%2Fblogger.googleusercontent.com%2Fimg%2Fb%2FR29vZ2xl%2FAVvXsEgCypzkb6uvHuNx6LKknUqtvQFoqsr6aalztDeBKT1aaUASzfjZMZAZqExx1k0w5iKWl08lx3MxbM_FwWxAvBdZODEerioaMp8OHVvhSjC8VL3uAW9_NMniMl_niggBVhVMdDFu2324YyhW5TrK4fua1PXlrb0DweOULvNgi5mlQUZUct_dIX3OePrfqks%2Fs1700-e365%2Fvalidate.jpg&w=3840&q=75)









_imageBROKER.com_Alamy.jpg%3Fwidth%3D1280%26auto%3Dwebp%26quality%3D80%26format%3Djpg%26disable%3Dupscale&w=3840&q=75)