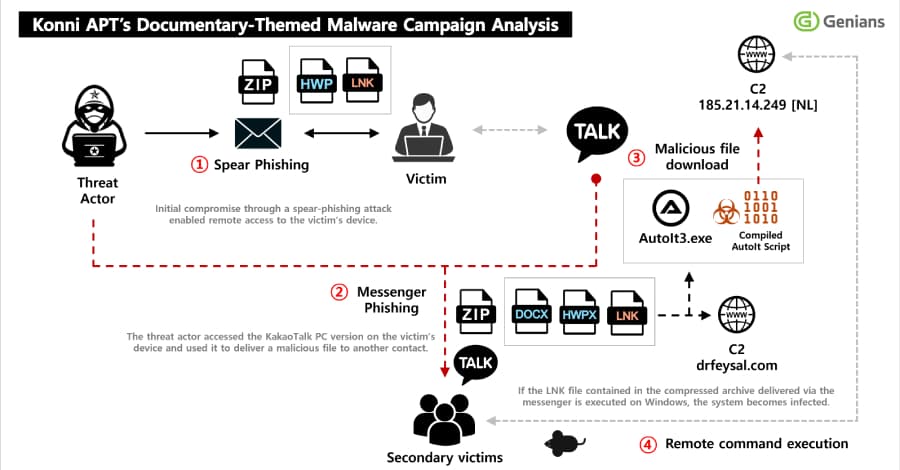
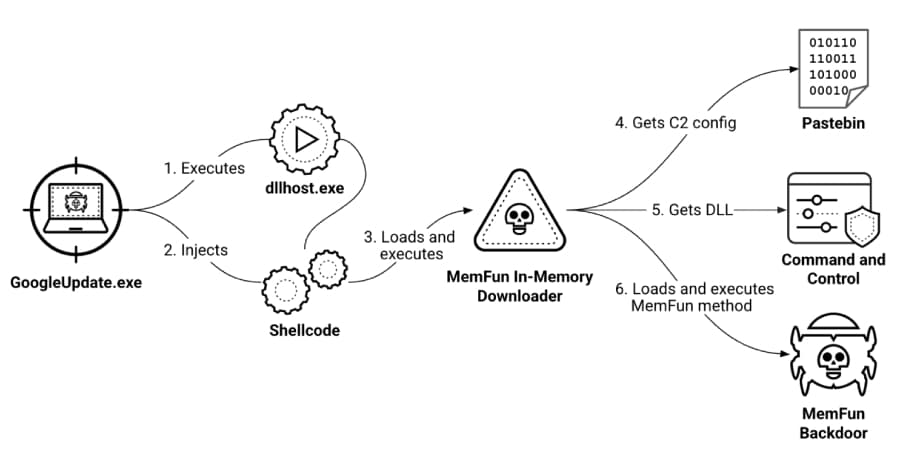
Konni Deploys EndRAT Through Phishing, Uses KakaoTalk to Propagate Malware
North Korean hackers have been seen sending phishing emails to get into people's KakaoTalk desktop apps and spread malware to some of their contacts This.
Konni Deploys EndRAT Through Phishing, Uses KakaoTalk to Propagate Malware
North Korean hackers have been seen sending phishing emails to get into people's KakaoTalk desktop apps and spread malware to some of their contacts This.














_Blackboard_Alamy.jpg%3Fwidth%3D1280%26auto%3Dwebp%26quality%3D80%26format%3Djpg%26disable%3Dupscale&w=3840&q=75)