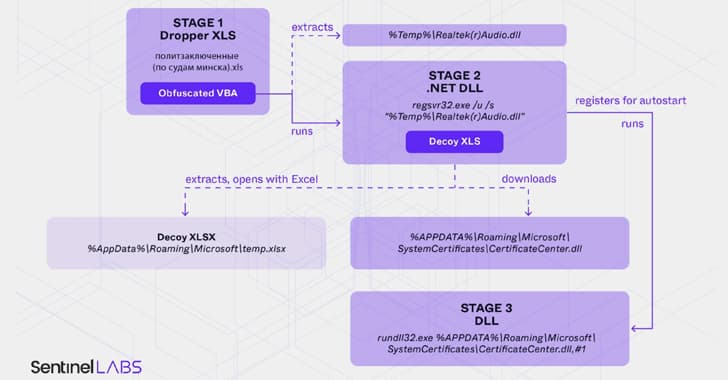
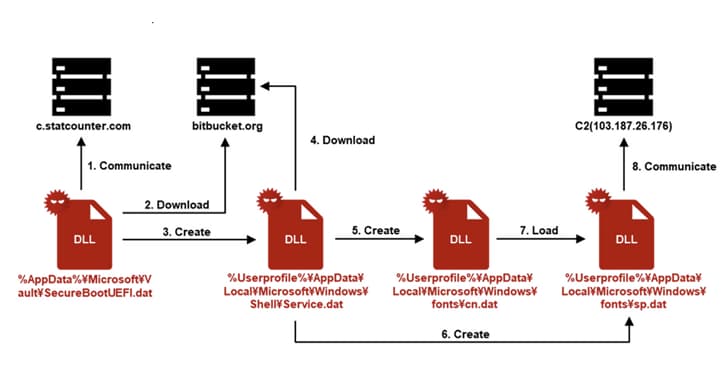
Belarus-Linked Ghostwriter Uses Macropack-Obfuscated Excel Macros to Deploy Malware
It has been determined that the threat cluster is an extension of an ongoing campaign carried out by a threat actor with ties to Belarus. An obfuscated macro is executed when a malicious Exce
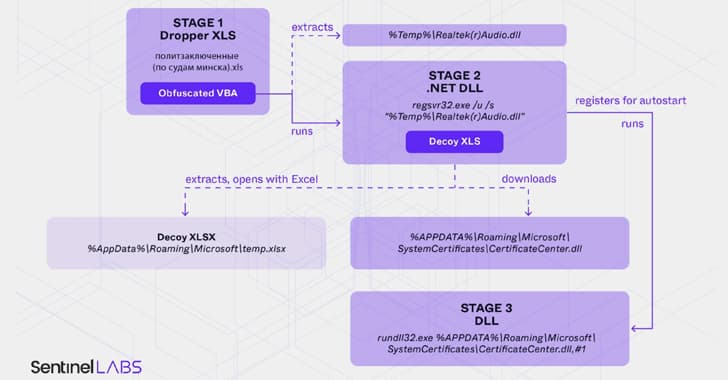
Belarus-Linked Ghostwriter Uses Macropack-Obfuscated Excel Macros to Deploy Malware
It has been determined that the threat cluster is an extension of an ongoing campaign carried out by a threat actor with ties to Belarus. An obfuscated macro is executed when a malicious Exce


![⚡ THN Weekly Recap: Top Cybersecurity Threats, Tools and Tips [6 Jan]](/_next/image?url=https%3A%2F%2Fblogger.googleusercontent.com%2Fimg%2Fb%2FR29vZ2xl%2FAVvXsEiKokWQpcRQ55ARtaBLhn4X9RCRcf5u5YW7JaJaQrIrcU6A96dBP2IS5th1jhuZX0cQMO04KAMOZDxqEIcPdkAqGmkXMpHzV7L_CECca3FJ_ppgWQh9J0y8D02mSQbw-nzuf-FzDIN412s_F2AO-MGpfr95e-yMTzPjQqkl-WKo8jY1o6XMVvnF7bEmngEk%2Fs790-rw-e365%2Frecap.png&w=3840&q=75)











